Integrated security systems
Design, deployment, and lifecycle support for CCTV Systems Qatar programs, unified monitoring, and evidence-ready recording.
Learn more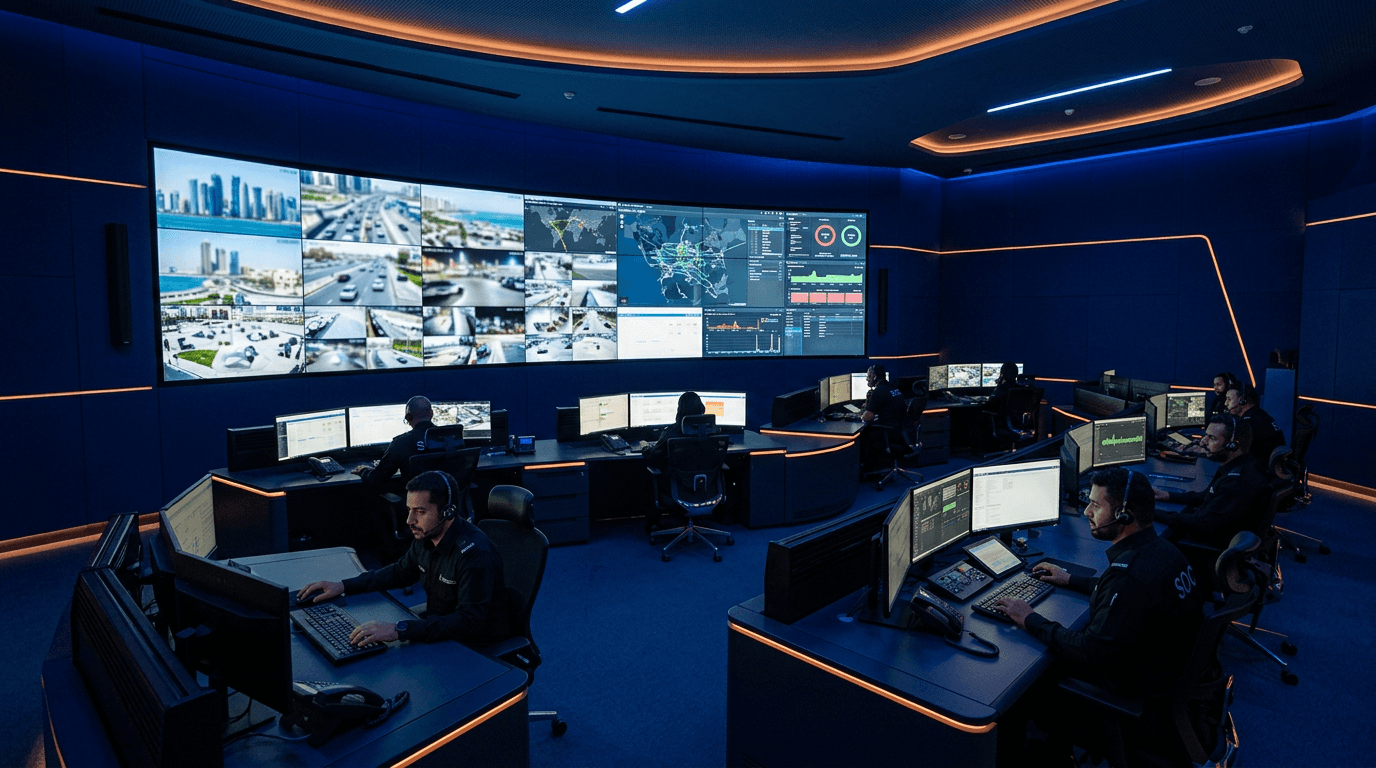
From Surveillance Systems Qatar rollouts to Access Control Systems Qatar integrations, we engineer dependable protection, resilient networks, and lifecycle support you can audit with confidence.
CTST combines field-proven delivery with clear documentation — so security, facilities, and IT teams stay aligned from design through operations.

End-to-end delivery for organizations that need clarity, quality, and measurable outcomes — not generic bundles.
Design, deployment, and lifecycle support for CCTV Systems Qatar programs, unified monitoring, and evidence-ready recording.
Learn moreAccess Control Systems Qatar deployments aligned to policies, visitor management, and audit-friendly reporting.
Learn moreResilient transport, structured cabling, and field services that keep critical sites connected end to end.
Learn moreHighlights that define how CTST supports Security Solutions Qatar programs across campuses, infrastructure, and public-facing sites.
Centralized visibility with disciplined alarm handling for faster decisions during incidents.
Quality-first installation practices for harsh outdoor environments and high-security facilities.
AMC, health monitoring, and roadmap planning so systems stay current after go-live.
Representative engagements demonstrating integration depth, field discipline, and long-term operability.

End-to-end surveillance and access orchestration for a high-footfall mixed-use destination in Lusail.
View project
Reliable video and perimeter awareness for distributed fuel retail locations with strict safety expectations.
View project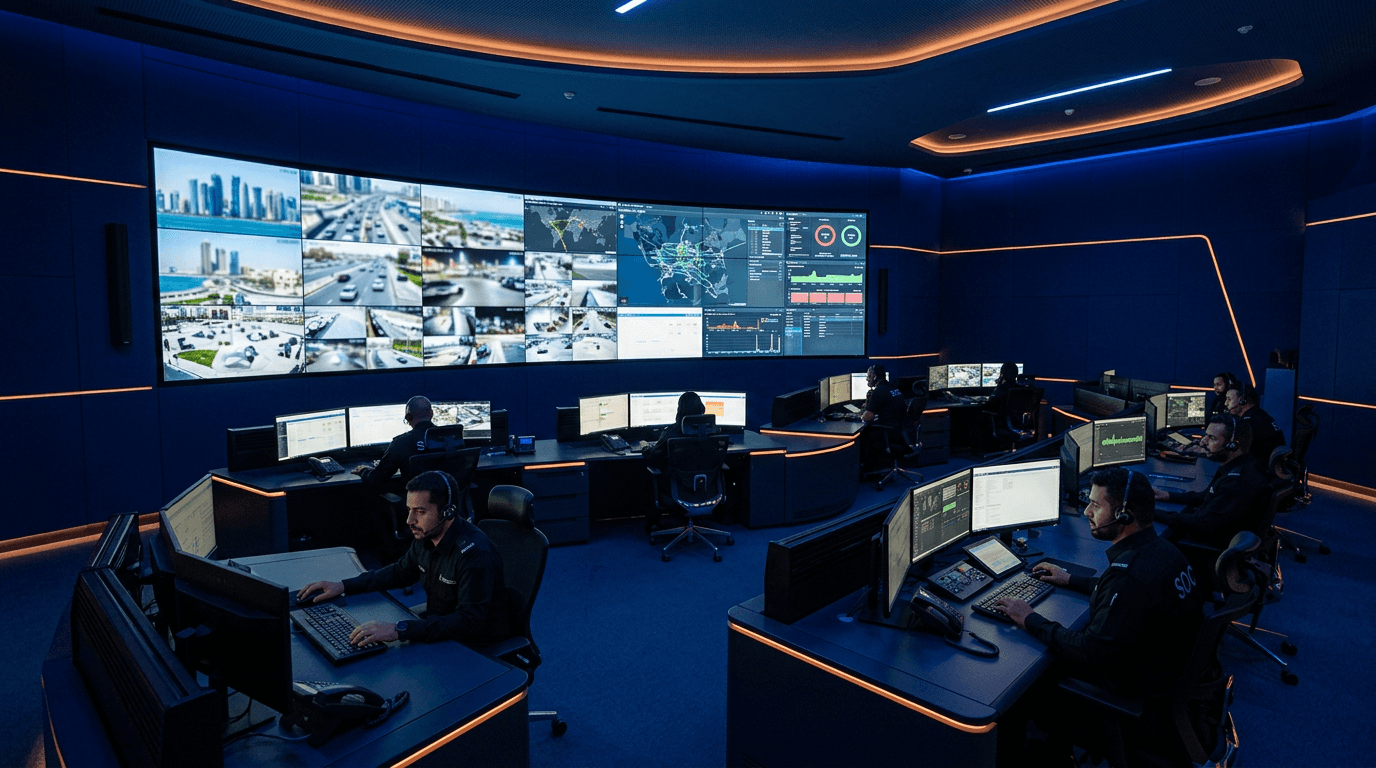
Structured AMC services to keep healthcare surveillance dependable, compliant, and audit-ready.
View projectWe integrate leading platforms and infrastructure components to match your standards, support model, and roadmap.
Practical guidance on network security, data protection, digital transformation, and privacy-conscious surveillance.

How to sequence identity, segmentation, and monitoring without stalling day-to-day operations.
Read article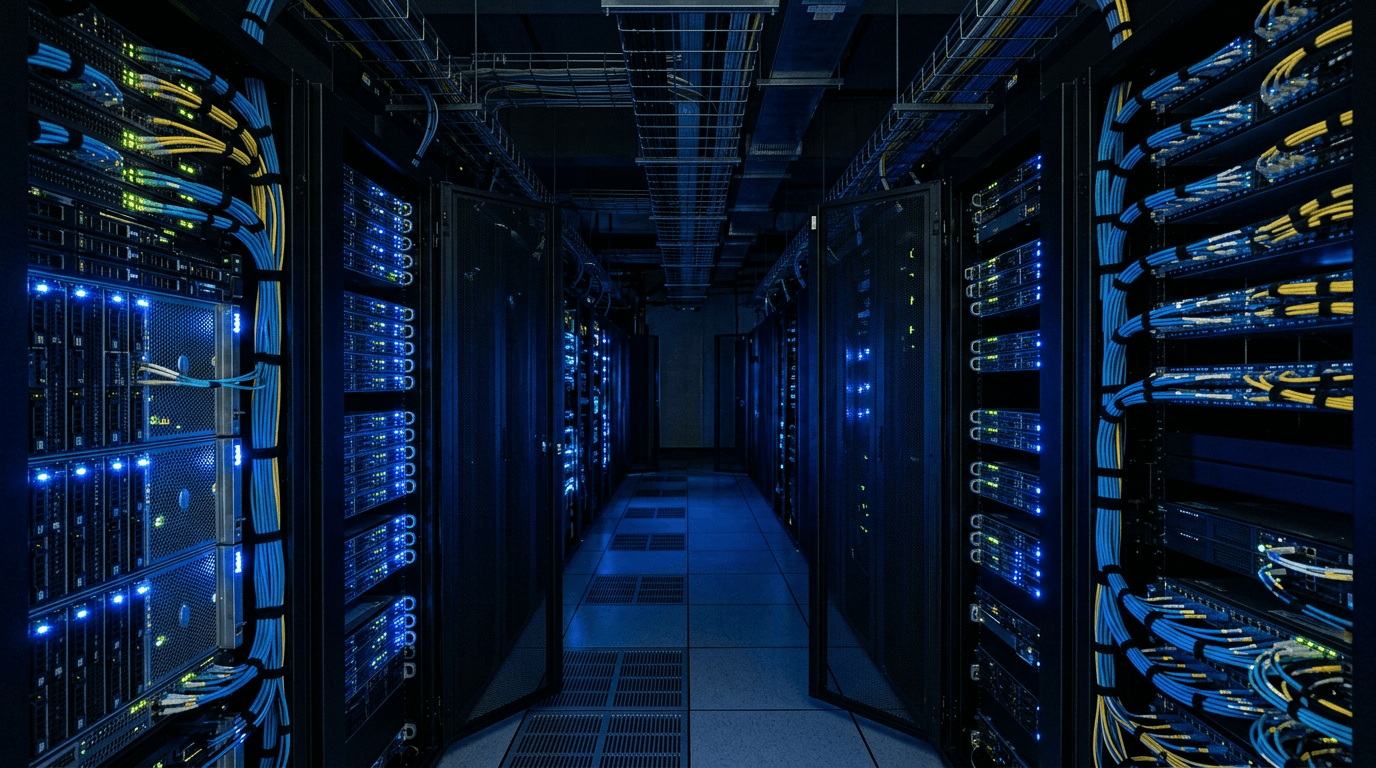
Design patterns that balance user experience with strong authentication and visibility.
Read article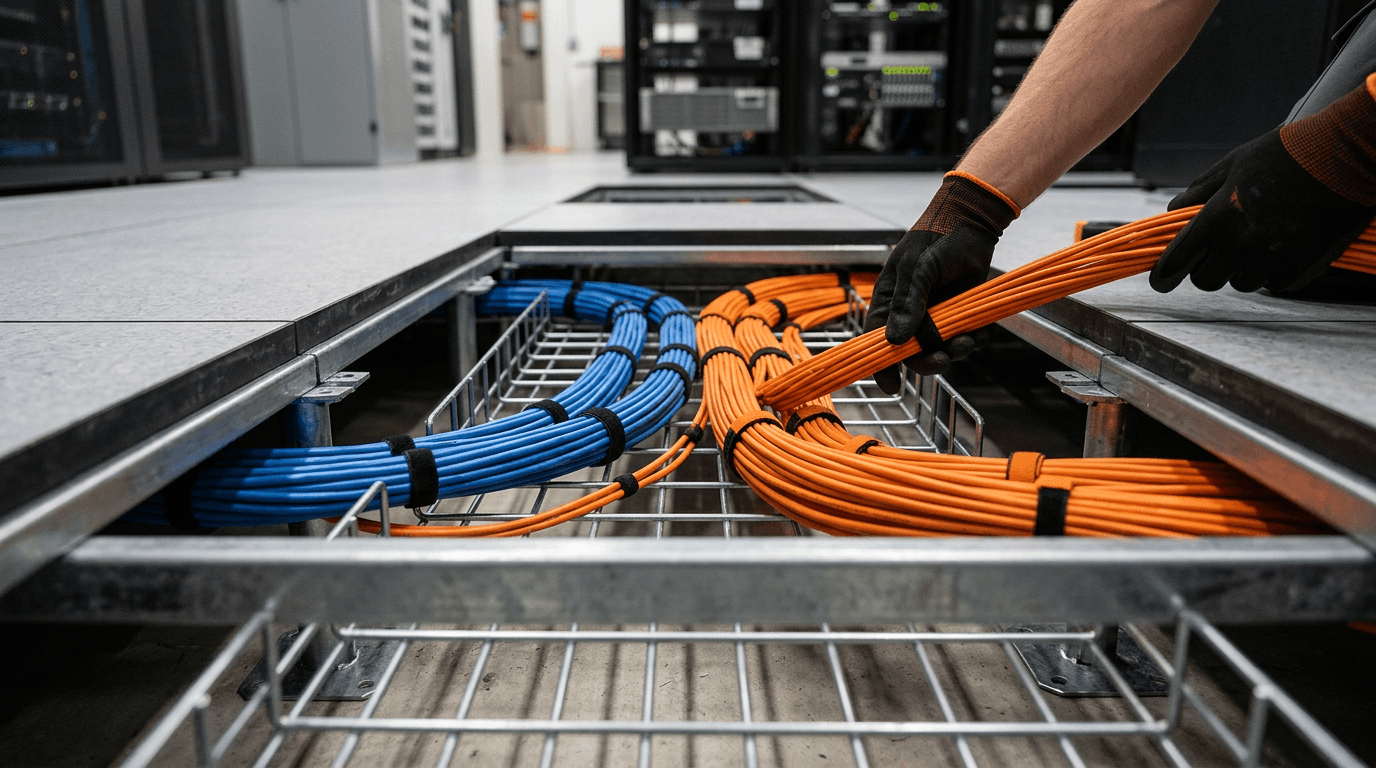
Reduce phishing success rates with layered controls and measurable outcomes.
Read articleTell us about your site, stakeholders, and timelines — we will propose a clear scope and delivery plan.