
A practical zero-trust roadmap for Qatar enterprises
How to sequence identity, segmentation, and monitoring without stalling day-to-day operations.
Read article
Practical perspectives for teams modernizing protection, connectivity, and governance — with SEO-friendly guidance you can act on.

How to sequence identity, segmentation, and monitoring without stalling day-to-day operations.
Read article
Design patterns that balance user experience with strong authentication and visibility.
Read article
Reduce phishing success rates with layered controls and measurable outcomes.
Read article
Segmentation strategies that keep industrial environments predictable and auditable.
Read article
Short scenarios, clear roles, and measurable improvements after every exercise.
Read article
A simple labeling model that scales and keeps DLP policies maintainable.
Read article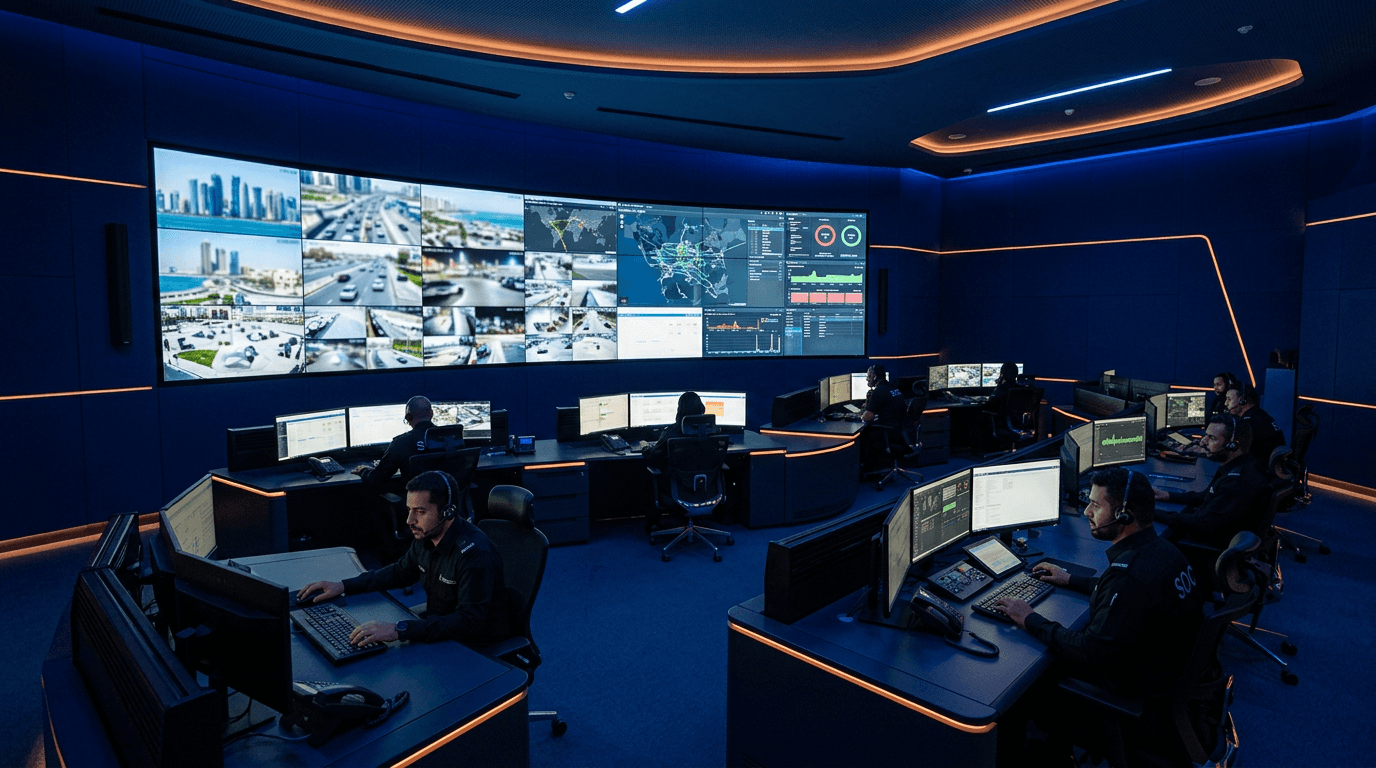
Balancing enforcement with productivity through context-aware rules and exceptions.
Read article
Transparent policies, proportionate monitoring, and supportive leadership messaging.
Read article
From unusual OAuth grants to bulk downloads—signals worth prioritizing.
Read article
Align legal holds, operational needs, and technical deletion with a single policy map.
Read article
Why bolt-on security slows programs—and how to embed controls from sprint zero.
Read article
Federation, lifecycle automation, and break-glass accounts done responsibly.
Read article
How mid-sized teams can professionalize requests without heavy ITIL overhead.
Read article
Hours saved, error reduction, and faster onboarding—numbers leadership respects.
Read article
Champions, training windows, and feedback loops that prevent silent non-use.
Read article
Data minimization, purpose limitation, and transparent signage as baseline expectations.
Read article
How to run DPIAs that surface real risks and produce actionable mitigations.
Read article
Security questionnaires matter, but evidence and contract terms matter more.
Read article
Fair processing notices, training, and escalation paths that reduce gray areas.
Read article
Workflows, identity verification, and redaction standards that keep timelines achievable.
Read article